Our Services
Tracing of Abuse Mails
We assist our company and personal customers hint the direction of any abusive email and forestall the threat with the ideal action. Our offerings assist groups save you any routine machine outages because of the malware connected to the e-mail. We additionally coordinate with the criminal government on behalf of our customers to ee-ebook the culprits.
Abuse mails or unsolicited mail have grown to be part of the internet. Though maximum of them are harmless, there are others that comprise malware together with viruses or adware and might reason foremost troubles if clicked on. These horrific emails are despatched beneath neath an identification created for that cause and via an internet course, this is close to not possible to tune via way of means of normal users. Spam is these days despatched via way of means of a software program known as spambots which are programmed to ship those malicious statistics. The bots create fake bills that can not be traced again to them to begin the sending process. The faux bills multiply in step with the wide variety of messages that want to be despatched. Tracking all such email ids isn't feasible for normal humans who've several different activities all through the day.
Spambots together with net crawlers accumulate the e-mail addresses from diverse reasserts on the internet, in maximum instances illegally. These can also additionally consist of the newsletters or updates recipients, particular newsgroups, visitor books, websites, forums, blogs, wikis, online organizations, or chat rooms, amongst many others. Once collected, the e-mail addresses are then both used for sending their very own unsolicited mail or given to different shady organizations who need to ship such messages. One number one cause for the proliferation of unsolicited mail is the easy coding layout of all emails which leads them to be very clean to find the usage of an easy software program program. The malicious programs use diverse techniques to cover their tracks. In positive instances, they mask their deal to reveal the identity notification of a person who's additionally a recipient in their unsolicited mail.
Besides normal unrequired messages that seem withinside the inbox in masses and are ordinarily harmless, there are different styles of emails that are some distance greater dangerous. These are created especially to goal an organization or a person via way of means of hackers or criminals and comprise malware which can reason havoc simply via way of means of being acquired withinside the inbox. Among the troubles, they invent consist of machine crashes, virus contamination throughout an inner network, statistics robbery inclusive of steady person identity notification and password stealing, and utilization monitoring. Though troubles together with monitoring the users’ online hobbies are practiced via way of means of almost all web sites to customize and simplicity humans’ interactions with their site, monitoring the behavior for malicious use later is a crook offense.
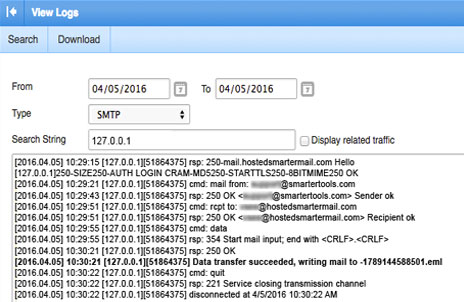
Tracing all such duplicitous online behavior calls for in-intensity expertise of the net, its infrastructure, and coding. We use diverse strategies to hint at the sender inclusive of analyzing the e-mail header. The header incorporates a maximum of the information vital to tune the message as every deal with or step withinside the direction is recorded. Our professionals also can pick out if a header has been manipulated in any manner to confuse the trackers. We additionally use diverse software program programs to run checks at the emails acquired which lets us locate the direction of the e-mail and its unique source. Once we pick out the source, we assist our customers to take all vital steps to dam the identity notification from sending any mail to them. In instances of particular targeting, we coordinate with the cybercrime cells of regulation officers to trap the culprits and ee-ebook them for criminal prosecution.

